 On the morning of November 17, 2024, something quiet and catastrophic happened beneath the Baltic Sea. A cable connecting Sweden and Lithuania went dark. Within hours, roughly a fifth of Lithuania’s internet capacity had vanished. Less than twenty-four hours later, another cable — this one linking Finland and Germany — was severed. Investigators focused their attention on a Chinese-flagged vessel, the Yi Peng 3, which had been transiting the region. Beijing initially denied involvement. Ten months later, it quietly admitted the ship was responsible, blaming bad weather.
On the morning of November 17, 2024, something quiet and catastrophic happened beneath the Baltic Sea. A cable connecting Sweden and Lithuania went dark. Within hours, roughly a fifth of Lithuania’s internet capacity had vanished. Less than twenty-four hours later, another cable — this one linking Finland and Germany — was severed. Investigators focused their attention on a Chinese-flagged vessel, the Yi Peng 3, which had been transiting the region. Beijing initially denied involvement. Ten months later, it quietly admitted the ship was responsible, blaming bad weather.
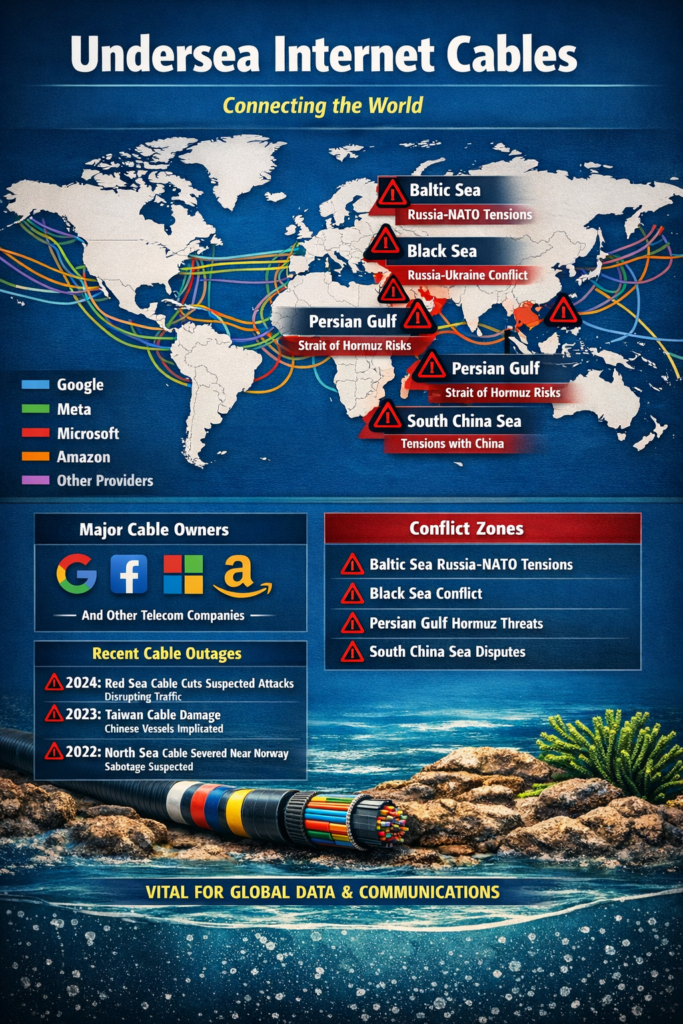
It was hardly an isolated incident. Since 2022, approximately ten subsea cables have been cut in the Baltic Sea region alone — seven of them between November 2024 and January 2025. Across 2024 and 2025, researchers at the cybersecurity firm Recorded Future documented 44 publicly reported cable damage events worldwide. Some were accidents. Many were not. And behind the ambiguity, security officials and telecommunications executives say, lies one of the most consequential and underreported power struggles of our era.
The fight over undersea internet cables — who builds them, who controls them, who can cut them — has quietly become one of the defining geopolitical contests of the 21st century.
THE INVISIBLE INTERNET
Most people have no idea that the internet, despite its reputation for ethereal cloudiness, is physically anchored to the ocean floor. Buried beneath nearly 1.4 million kilometers of seawater are fiber-optic cables no thicker than a garden hose, carrying virtually every email, financial transaction, video call, and military communication that crosses an international border. When they are damaged, consumers do not usually see “cable cut” on their screens. They simply find that the application they are trying to reach has become unbearably slow — or unreachable entirely.
For decades, these cables were the unglamorous province of telecommunications consortiums, quietly maintained and largely ignored by governments and the public alike. That era is over. The seabed, as one U.S. national security analyst recently put it, “is no longer a passive frontier. It is a contested battlespace.”
RUSSIA’S SHADOW FLEET
Russia has been the most brazen actor. In December 2024, a vessel departing from the Russian port of Ust-Luga dragged its anchor across ninety kilometers of the Gulf of Finland, severing five cables and inflicting an estimated €60 million in damage. The maneuver was technically deniable — ships drag anchors, after all — but the scale and precision were difficult to attribute to accident alone.
This is the signature tactic of what analysts call “gray zone” warfare: actions calibrated to fall just below the threshold of a formal military response, while achieving real strategic damage. Russia has spent years mapping critical undersea infrastructure in the North and Baltic Seas, a campaign documented in a sweeping 2023 report by Swedish intelligence. The country operates a fleet of research and espionage vessels — most prominently the Yantar, a ship that has been tracked loitering over cable routes on multiple occasions — capable of both surveilling and, potentially, severing the cables beneath them.
In 2023, former Russian President Dmitry Medvedev made the threat explicit, warning publicly that if the West was behind the Nord Stream pipeline explosions, Moscow would have no moral constraints remaining against destroying adversaries’ undersea cables.
CHINA’S DIGITAL SILK ROAD
China’s approach is, in some ways, more ambitious — and more unsettling to Western officials. Rather than simply threatening cables, Beijing has been methodically building them. Through state-backed firms like HMN Technologies (formerly Huawei Marine Networks, rebranded under pressure), China has been financing and constructing undersea cable projects across Africa, Southeast Asia, and the Middle East, positioning itself as the indispensable contractor for the developing world’s digital connectivity.
The strategy is a maritime extension of the Belt and Road Initiative: offer favorable financing, deploy cheaper technology — HMN Technologies prices its systems at roughly 20 to 30 percent below Western competitors — and quietly embed influence into the infrastructure that a nation depends on for its economic life. Cables built by Chinese companies can, in theory, provide Beijing with access to the data flowing through them, or the leverage to disrupt that flow entirely.
The contrast between two cables currently racing toward completion illustrates the stakes precisely. The PEACE cable — built by HMN Technologies, backed by Chinese capital — bypasses India entirely and makes stops across Africa, creating a connectivity corridor that aligns almost perfectly with Chinese strategic interests. The SEA-ME-WE 6 cable, built by U.S.-based SubCom and backed by a 16-member Western consortium, runs instead through India and key Gulf economies. Both connect Asia to Europe. Neither is merely about internet speeds.
Red Sea disruption, February 2024: Houthi military operations in the Red Sea damaged multiple undersea cables, disrupting internet access across East Africa and parts of Asia. The incident underscored how geopolitical flashpoints on the surface translate directly into digital vulnerabilities below — and accelerated U.S. and allied efforts to route new cables away from contested straits and chokepoints.
BIG TECH’S PRIVATE OCEAN
Into this geopolitical vacuum has rushed a third force that nobody anticipated twenty years ago: Silicon Valley. In 2010, Google, Meta, Microsoft, and Amazon had collectively invested in exactly one long-distance undersea cable. By 2024, they owned all or portions of more than thirty. Meta recently announced Project Waterworth, a planned 50,000-kilometer cable system — the longest ever built — that will connect the United States to India, South Africa, Brazil, and other markets across the Southern Hemisphere. The route is deliberately engineered to avoid the Red Sea, the South China Sea, and other geopolitical flashpoints. A person familiar with Meta’s planning told TechCrunch the project was designed specifically to “avoid areas of geopolitical tension.”
The tech giants’ motivations are commercial — owning cables means faster, cheaper data transfer between their own data centers — but the geopolitical implications are profound. These companies are now, effectively, private infrastructure powers, making decisions about where the internet’s physical backbone runs that once would have been the exclusive province of national governments. The question of who controls global connectivity can no longer be answered without mentioning Mark Zuckerberg and Sundar Pichai alongside the leaders of the United States and China.
Not everyone is comfortable with that shift. Researchers at the Open Markets Institute have warned that the vertical integration of content and cable infrastructure by four U.S. corporations creates new forms of monopolistic risk — and new vulnerabilities. Governments, they argue, could respond by treating cables as public utilities subject to regulation, or by investing in alternative, publicly owned routes.
THE REPAIR PROBLEM
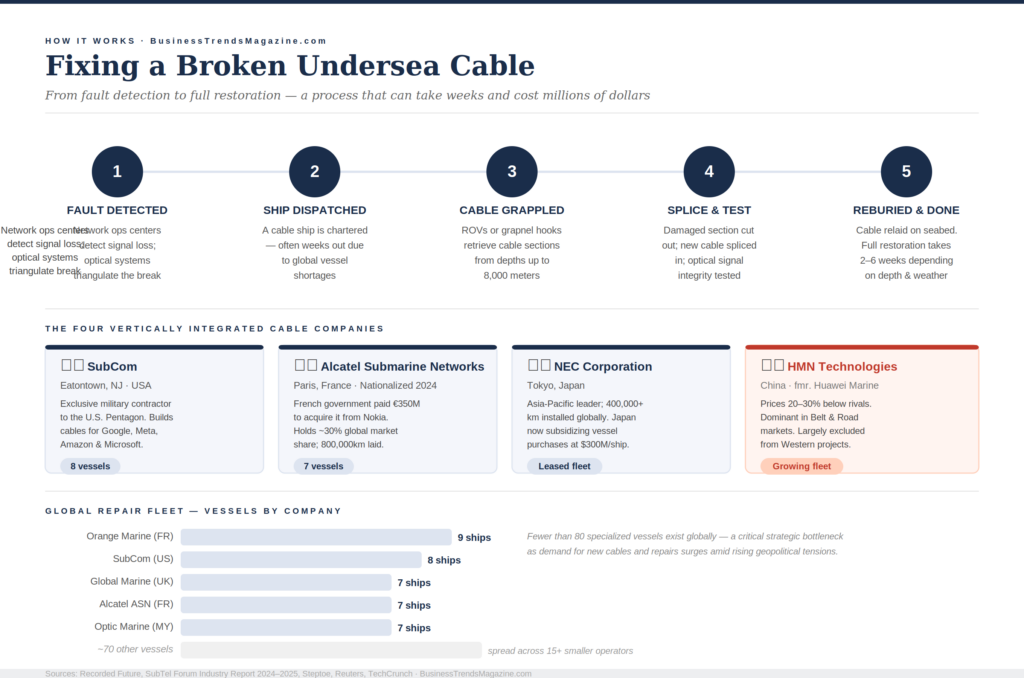
Beneath the strategic maneuvering lies a more mundane and arguably more alarming vulnerability: when cables break, the world has very few ships capable of fixing them. Fewer than 100 cable repair vessels exist globally. In the Baltic and South China Sea — precisely the regions where tensions are highest and cables most at risk — Chinese state-linked repair companies dominate the market, and they have been documented operating with opaque vessel-tracking, delaying repairs in sensitive regions, and concealing their locations from satellite monitoring systems.
The repair bottleneck is not accidental. It is a strategic lever. A state that can delay the restoration of a rival’s severed cable — through bureaucratic obstruction, market dominance, or simple unavailability — wields a quiet form of power that almost no international treaty governs.
WHAT COMES NEXT
The response from Western governments has been accelerating, if still fragmented. NATO has deployed approximately fifty drones as part of its “Task Force X” initiative to monitor suspicious maritime activity in the Baltic, and is weighing a similar program in the North Sea. The United States has pushed to restrict Chinese companies from participating in major cable projects in the Pacific and is coordinating with allies to ensure new routes are built by what officials call “trusted partners.” Japan has long maintained a multinational cable-repair coordination agreement in the Asia-Pacific region. Australia recently funded a cable to Papua New Guinea specifically to prevent the island nation from falling into dependence on Chinese infrastructure.
The Biden and Trump administrations alike have signaled a willingness to expand U.S. development finance to counter Chinese cable investments — a proposal that could see the Development Finance Corporation’s funding capacity grow from $60 billion to as much as $250 billion.
But the fundamental challenge is structural, and it will not be solved by surveillance drones or diplomatic pressure alone. The undersea cable network was built for commerce, not conflict. It was designed by engineers optimizing for bandwidth and cost, not by strategists thinking about chokepoints and sabotage. Entire island nations — Malta, Cyprus, Iceland — depend on a small number of cables for their full connectivity to the global economy. Sever the right link in the right place, and a country does not go dark dramatically; it goes dark quietly, link by link, as traffic reroutes until there is nowhere left to go.
The next great power confrontation may not announce itself with missiles or cyberattacks. It may announce itself the way November 17, 2024 did: with a ship, an anchor, and a cable that simply stops responding — somewhere in the cold dark water where no one is watching.
Sources: Recorded Future Insikt Group, TeleGeography, CSIS, University of Washington Jackson School of International Studies, Bloomberg, Oxford Internet Institute, TechCrunch, Open Markets Institute, Truman National Security Project.


